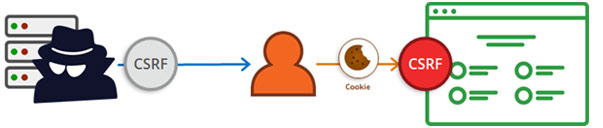
CSRF (Cross Site Request Forging) Vulnerability
ATTACK
CSRF stand for cross-site request forgery. It is where the attacker sit can remotely, create a dummy form, and submit it via a valid session of a user who is already logged in either via a chat application or a phishing attack. There are basically 2 ways by which this attack can be performed. First is, where the attacker tricks the victim to click a link or load a page. This is basically done by social engineering and malicious links. The second part is where the attacker sends a crafted, legitimate-looking request (Trojan) from the victim?s browser to the website.
As the name of the attack suggests this forgery is possible only after the request is granted i.e. when the following assumptions are fulfilled:
1) Valid session.
2) Form parameters.
3) Timing of the session execution on the same browser.