SIEM Implementation
Overview
SIEM : Security information and event management (SIEM) provides real-time analysis of security alerts generated by network hardware devices and applications. SIEM is not just a product or service, but is a correct combination of software, appliances or managed services, and report producing tools.
Some Facts
Security Management :
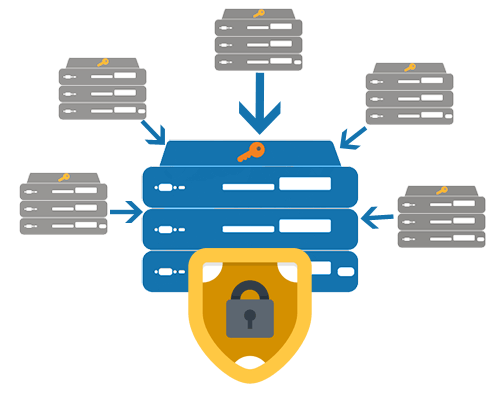
SIEM primarily deals with real-time monitoring, event correlation and notification, while providing long-term storage, analysis and reporting of log data. The key focus is to monitor and help manage user and service privileges, directory services and other system configuration changes; as well as providing log auditing and review and incident response.
Capabilities of SIEM solution