How to test android app security
At the device level, there are 2 ways in which the application shall be tested.
- With Android device running in a factory default or normal mode
- With Android device running in a rooted mode
At the application level, there are 2 ways in which it shall be tested
- Application running on the device (to take benefits of touch related features)
- Application running on the emulator (to ease the task of testing using wider screen of desktop or laptop)
When your Android app is uploaded decompiles it, and tests the client layer of the app against a rules based engine that uses static analysis to find the security vulnerabilities and flaws of the app.
The android app checklist is split into five different fields:
Store specific checks.
App User interface checks.
Network specific checks
Device specific characteristics. These are characteristics that are related to the device on which the app is installed.
App checks. These are things to check that have to do with functionality that is frequently used in an app.
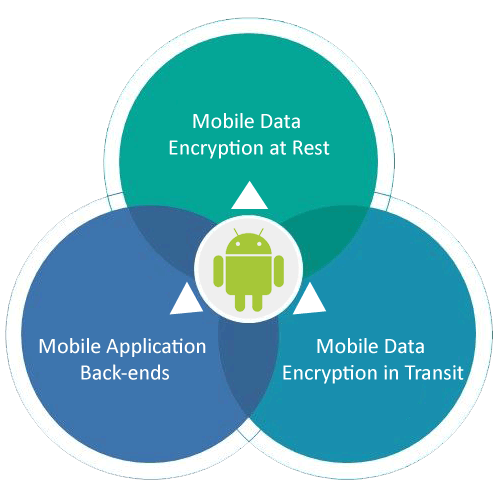
The fundamental objective of android app security testing is to ensure that the application's data and networking security requirements are met as per guidelines. The effective test planning in Mobile Application testing makes helps to improve the quality of Mobile Apps. In this article we are exploring how to achieve the mobile application quality and get better competence on mobile testing.