Ensuring Security On Open Source Virtual Platform
We must thank IT virtualization as it led us to cloud technology. Today's IT infrastructures are already running their mission critical business applications on virtual machines.
Like the physical infrastructure, virtualization is also cursed with cyber security challenges. This article talks about a typical open source virtualization solution and depicts the steps to secure its.
Virtualization Architecture
As we know, a virtual server is a resource based instance of an operating system. It consumes the pre-configured amount of CPU speed, memory and disk space from the physical hardware. An important low level software component called as HAL (Hardware Abstraction Layer) sits in between the physical hardware and the operating system. HAL is responsible to convert OS calls into a set of CPU instructions and vice-versa, thus enabling high level application stack to run smoothly. HAL also makes the OS independent of the hardware components, hence makes it portable across multiple physical platforms.
Virtualization is achieved by adding another low level software layer along with HAL, which allows us to simulate multiple virtual machines on a single physical machine, whereby each virtual machine can run its own copy of operating system. Since this layer is working together with HAL, it provides great flexibility for us to select operating system, assign dedicated CPU and other resources to a particular machine etc.
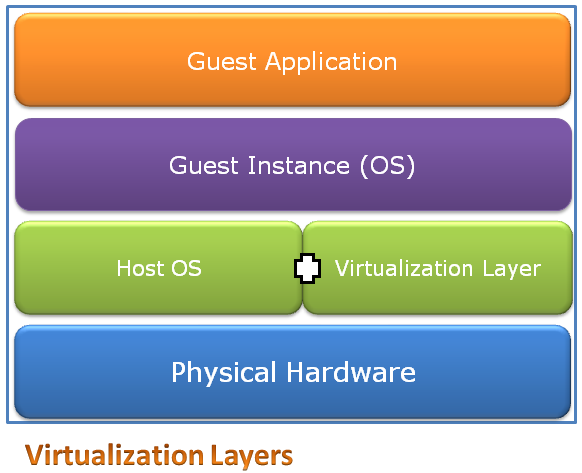
Fig 1. shows basic building blocks of virtualization architecture. A component called virtual session manager is runs in parallel with the guest instances in order to allocate system resources and monitor the usage. In theory, there are three types of virtualization. First type is called as hypervisor which also mean fully virtual, wherein all guest instances are kept separate from each other. In the second type called as para-virtualization, the guest systems know about each other. This is achieved by semi-abstraction of physical and OS layers. The benefit in this method is that it takes lesser toll on the system resources to result into faster guests, but compromises on the security. The third type is called as OS level virtualization in which the abstraction layer simulates multiple instances of the host OS. Hypervisor is the most famous type of installation.
Xen Open Source Virtualization
As we all know, the open source world is blessed with Xen server which provides all great features of an industry standard hypervisor technology. Xen server allows us to create multiple guest instances and seamlessly schedules the CPU time, partitions memory spaces. The Xen architecture contains 3 main components, the hypervisor layer, domain manager and the guest instances. Xen domain manager is a kernel component which runs before any other guest instance can be started. It provides functions such as allowing creation of child domains, creating and managing virtual devices for guest domains and also to control network and disk resources. Guest instances are not allowed to access hardware resources directly, in fact they communicate to domain manager through proxy calls to ask for access. They also update the domain manager about their online or offline status.
Securing Open Source Virtualization
As we discussed earlier, the operating system HAL layer and hypervisor components work hand in hand to achieve virtualization. However it also means that invasion of any of these components can effectively make the entire virtual layer and guest instances vulnerable to cyber attacks. It is very important to keep in mind, that virtualization is a software component and can be affected by programmatic as well as man-made cyber attacks, just as any physical server infrastructure. Securing a virtual infrastructure is effectively securing each of the layers that form it. Lets first talk about typical attacks which can render a virtualization infrastructure in-secure.
Hypervisor attacks
This is a serious type of attack whereby the attacker exploits a vulnerability of the hypervisor layer which communicates with the HAL and guest operating systems, thus infecting the entire infrastructure hosted on a physical server. There are viruses which are specifically designed for this purpose. The most critical moment of causing hypervisor infection is during the installation phase.
Guest OS security
From a system administrator's point of view, the virtual machines are pretty much the same as physical servers. Hence all the security management techniques of physical machines apply to the virtual guest machines too. Leaving guest operating systems un-patched or not performing a correct security lockdown can result into serious vulnerabilities.
Guest communication security
It is highly likely that guest operating systems hosted on the same virtualization infrastructure will communicate with each other. This TCP communication is usually routed through a redirector service which is part of the hypervisor layer. Hence there is no packet transmission happening on the physical network card of the physical server hosting infrastructure. While this improves the communication speeds, it introduces a limitation whereby the intrusion detection systems cannot detect the network layer problems. This problem needs to be addressed correctly; else it can make serious vulnerabilities invisible to the security monitoring.
Guest hopping attack
In this type, the attacker can gain control of one of the guest virtual instance, and then make use of a famous exploit called as hypervisor escape. This vulnerability can let attacker traverse from one guest system to another, called as guest hopping, thus infecting the whole infrastructure. This attack is usually used to create zombie machines which are then used to plant a distributed denial of service attack.
Management console attacks
Each virtualization infrastructure provides a web based console interface for administrator to add/remove machine resources or to monitor the guest operating systems. This console can introduce web layer attacks, which can help attacker gain control of the virtual infrastructure.
Hyperjacking
In this rare type, the attacker gains control of the physical host and creates a bogus virtual machine. Alternatively the attacker can get hold of an existing test virtual instance which is deployed during the initial installation phases. Such instances are usually ignored and hence left un-patched, thus making it a vulnerable component. Attacker can make use of such a machine to his evil benefits. Besides these attacks which are specific to virtualization servers, other attacks such as authentication attack, man in the middle, packet crafting, denial of service etc apply too.
Virtualization Security
Following table shows various system components of virtualization infrastructure and the corresponding security layers required for end to end security.
| Virtualization Layer | Security Implementation |
| Physical Host | Physical security Firewall Intrusion Detection System |
| Host OS | OS hardening Access control |
| Virtual HAL | Install from genuine source Avoid stray instances Apply security patches |
| Guest OS | OS hardening Access control Patching |
| Guest Application | Application level security installations and controls |
Implementing security for a virtualization infrastructure is a methodical and multi-step process. We need to begin with physical infrastructure, the installation and hardening of operating system on it. If Xen server is being installed from scratch, getting an infection free copy of the distribution is critical. The next step is to configure user level security, enabling access only to the administrators, to create or delete or modify the guest operating systems. It should be ensured that no stray guest instances are left lingering on the infrastructure, and should be deleted if found. While configuring guest operating systems, it is important to remember that each instance may run a different make or version. Hence a unified patch management solution which can cater to heterogeneous systems needs to be deployed. The same goes true for the antivirus software.
Besides patching, each OS should be hardened and configured for correct security accesses. As mentioned earlier, the communication between guest instances is not visible on physical network interface; hence an intrusion detection system should be deployed. The correct way to do this is to dedicate one guest instance on each virtual infrastructure for the purpose of packet sniffing and intrusion detection. Physical security for virtual servers is very crucial this is because stealing a physical machine means stealing more than one virtual machines, thus resulting into serious data theft or infrastructure breakdown. For virtual machines hosted in de-militarized zone, proper perimeter defense system comprised of firewalls and UTM devices should be deployed too.

