Steps: ⦁ I used a vulnerable website (⦁ http://testhtml5.vulnweb.com/#/popular) a)Pre-settings to be done b)Go to the vulnerable website: c) Do Forget password: ⦁ I have…
Day: January 6, 2020
WordPress VAPT And Fixation Techniques
VULNERABILITIES FIXATION TOOL USED FOR SCAN – WPSCAN. PLUGIN USED FOR FIXATION Full path disclosure: Many websites running WordPress are exposing the internal path/full path…
Vulnerability Assessment in 3 PHP Frameworks
Vulnerability Assessment in 3 PHP Frameworks PHP is the most widely used server side language to build web applications and has a good variety of…
Top 10 Web Log Analyzers
Title: Top 10 Web Log Analyzers Scope of article Today’s web hosting data centers are deployed with multiple web servers, running heterogeneous operating systems architecture….
Top 10 Security Vulnerability Scanners
Title: Top 10 Security Vulnerability Scanners Scope of article Gone are the days when a network administrator would sit in his cozy datacenter room, sip…
Top 5 Security Assessment Tools
Title: Top 5 Security Assessment Tools While performing a vulnerability scanning against a network, it needs to be done from within the network as well…
Top 3 Network Monitoring Tools
Title: Top 3 Networks Monitoring Tools Scope of article In a well managed IT infrastructure, network monitoring acts as eyes and ears to spot problems…
SOC2 Compliance for Startups
SOC 2 FOR SERVICE ORGANISATIONS SOC for Service Organizations reports are designed to help service organizations that provide services to other entities, build trust and…
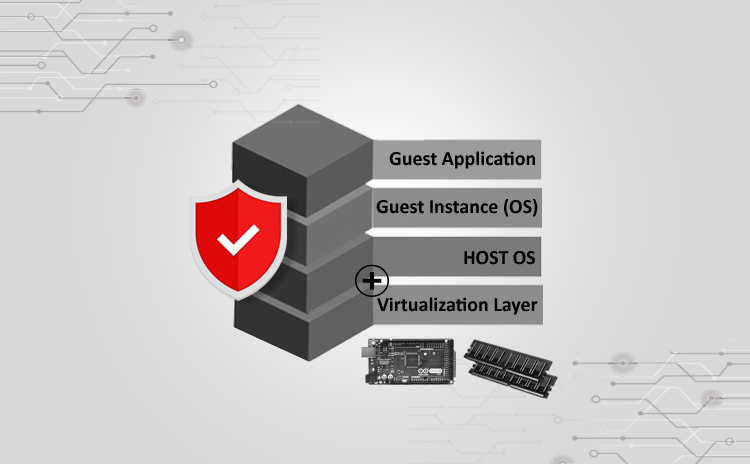
Securing Xen Virtualization
Title: Securing Xen Virtualization Scope of article The concept of virtualization was created in IT industry to achieve easy management and maintenance of the server…
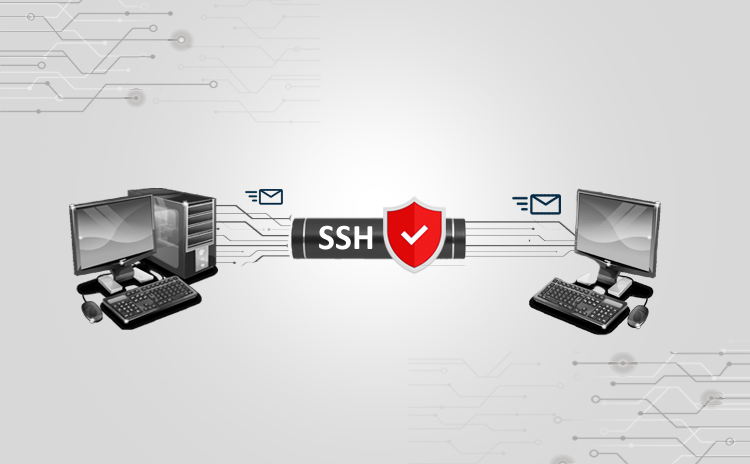
Securing SSH Service
Title: Securing SSH Service Scope of article SSH service is very widely used in the open source infrastructure setups. Due to its small footprint on…