Open Source Security Tools Tripwire
With the increasing demand of cyber security in open source world, it has become important to know all the methods and tools available. There are many tools available, which can either be used manually, or embedded in a script to perform the automated security related tasks.
With this article we are starting a mini-series of such security tools, where we will talk about small and useful security utilities available for open source systems. These tools are meant for system and network administrators, to help them strengthen their IT infrastructures.
As we all know, cyber security is never hundred percent, but in fact a continuous improvement process. In the past issues, we covered cyber attacks in details which laid out a ground for understanding security fundamentals. We learnt that there is no single utility, commercial or open source, which can fix all the vulnerabilities and make IT infrastructure secure from attacks.
We also understood that implementing an intrusion detection system is imperative for an IT infrastructure, besides the bells and whistles already in place. For each vulnerability or attack vector, there are multiple utilities available which help network administrators implement, monitor and audit the cyber security. Many famous utilities or tools such as Nmap, Chkrootkit, Snort etc are already covered in details. This series brings to the readers those tools which are not known or at least not commonly known. The first in the series is Tripwire.
Tripwire
In the continuously changing IT infrastructure, it is important for a system administrator to know if and when a file structure is changed. Such a change can stem out of a regular code release, or can be a malicious file update caused by viruses, spywares or root-kits. This calls for a detailed file update monitoring and logging. Tripwire is an open source tool available for all Linux distros just for this purpose. It detects and reports any unauthorized changes to the files and directories. Now let's understand in details how the tool works, and the methods to install and use it effectively.
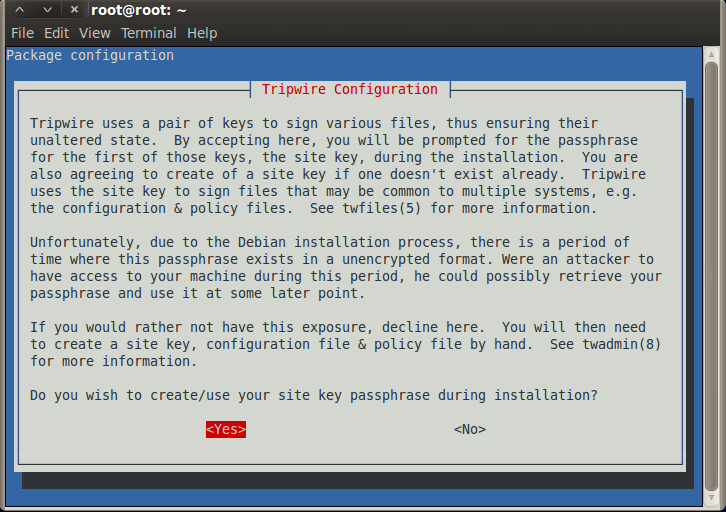
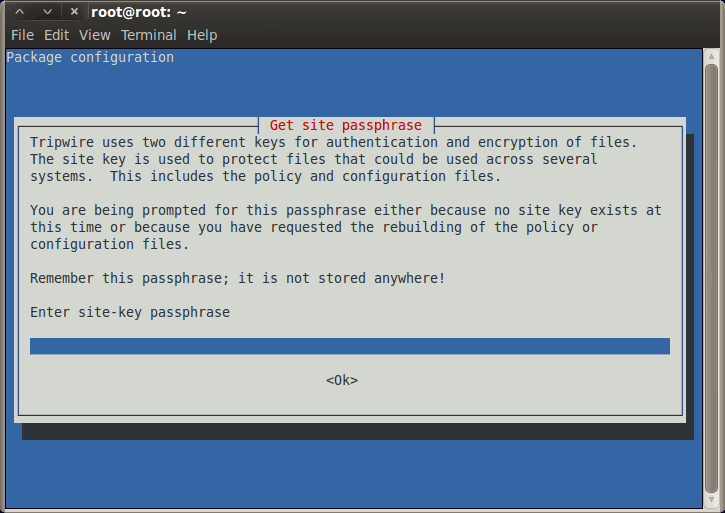
At a high level, Tripwire works on a "sample and compare" way. When Tripwire is installed and run for the first time, it scans the entire file system, to create a database. This database contains information about file structure as well as date and time stamp and other vital parameters for each file. System binaries as well as user application files are scanned and their information is stored in the database. At this point Tripwire enters into a monitoring mode and keeps a watch on every file access and especially the update. Each update is compared with the referential database, and intelligent actions or alerts are generated out of it. Tripwire monitors and detects file additions, deletions, updates etc, and also watches for files attribute changes. If the changes are legitimate, the administrator can update the tripwire database to accept these changes. The contents of this baseline database are indeed supposed to be secure. Tripwire asks for a site key, which is a sort of password that needs be entered by administrator while installing tool for the first time. Though this is an optional step, it is highly recommended to do so. This site key encrypts the database and decrypts it on the fly, while performing a comparison with file system scan results. During installation phase, the site key resides on the machine itself in a plain-text form, however after installation is complete, it is removed, prompting the installer or administrator to remember it, just like a password.
Now let's see how to install Tripwire. Being a sourceforge project, you can download Tripwire from their website at http://sourceforge.net/projects/tripwire. The easiest way to do so on Ubuntu or Backtrack distro, is to run command apt-get install tripwire. Please refer to the screen shot where Fig 1. shows the first screen of installation. It clearly mentions exactly what Tripwire does, and the security required around the site key. Fig 2. shows screen where the tool is asking installer to enter a pass phrase, which is nothing but the site key as mentioned above.
Running Tripwire
Once the installation is complete, it's important to understand files created by the tool and the command sets. While the man pages explain everything in detail, the table below depicts four commands that every administrator must know. Also mentioned in the table, are three user manual references that Tripwire installation creates, which explains each component of the tool in details with various command line options.
While configuring Tripwire, it is critical to understand about Tripwire policies. After the default installation every administrator would want to tune the tool based on his network scenario. Each object in policy file is associated with a property mask, which describes what changes to the file or directory Tripwire should monitor, and which ones can safely be ignored. This fine-tuning helps the system administrator to closely control how the tool should check integrity of a file system. Policy configuration is usually a one-time task and can need an update only if the infrastructure or the configurations change drastically.
A policy sets the rules in the format object_name -> property_mask. Here the object name is a fully qualified path to a file or directory and the property_mask specifies what property to examine or skip. As an example, if we want the tool to scan entire /var/log folder and files, except the mail.log, the policy would be set as below.
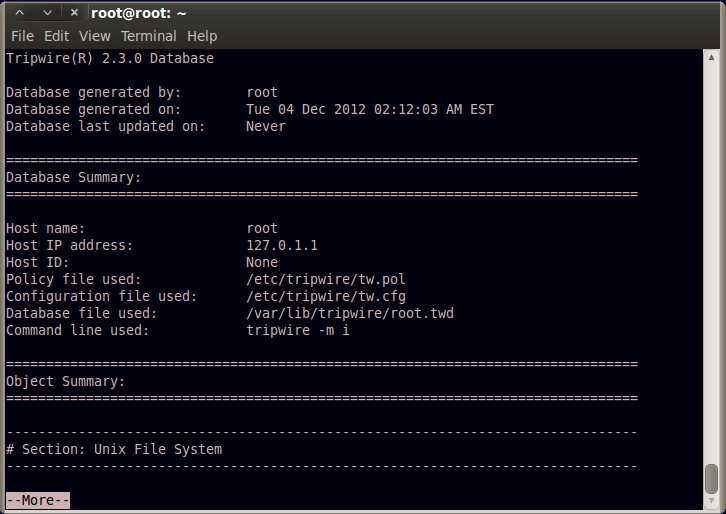
Please refer to the man pages of twpolicy to understand powerful setting options. Fig 3. shows screen where Tripwire is run in interactive mode, which also shows the locations of policy and configuration files that can be tweaked by administrators as per their needs.
As we saw, Tripwire is a complete command line operated host based intrusion prevention tool. Administrators can run it using a cron job and grep and parse its output to generate alerts. In a mid size IT infrastructure, by using proper user permissions, Tripwire can scan all servers and save logs on a centralized database for future attack analysis, or for compliance reasons. Large organizations can make this tool part of their code release management cycle. This can help avoid situations where a code is inadvertently overwriting a system or critical application file, thus improving the post-installation stability. The tool can be used to ensure integrity of plain-text databases too, which are usually found on older Linux systems.

