What are risk assessment and risk treatment? and what is threat intelligence? is there any difference between the two? if yes, what is the difference?…
What is the ideal web session timeout?
One of our customers for whom we had performed Mobile App VAPT asked us, what should be the ideal session timeout for their FinTech App?…
Less known features of Nmap Tool
Introduction As an information security professional, you need to scan network devices and servers to know more about the security vulnerabilities in networks. In this…
Go For ISO27001:2022 Immediately or Wait?
After almost 9 years, ISO27001 new version 2022 is released and I am not surprised that there is a big hoopla about it. Industry was…
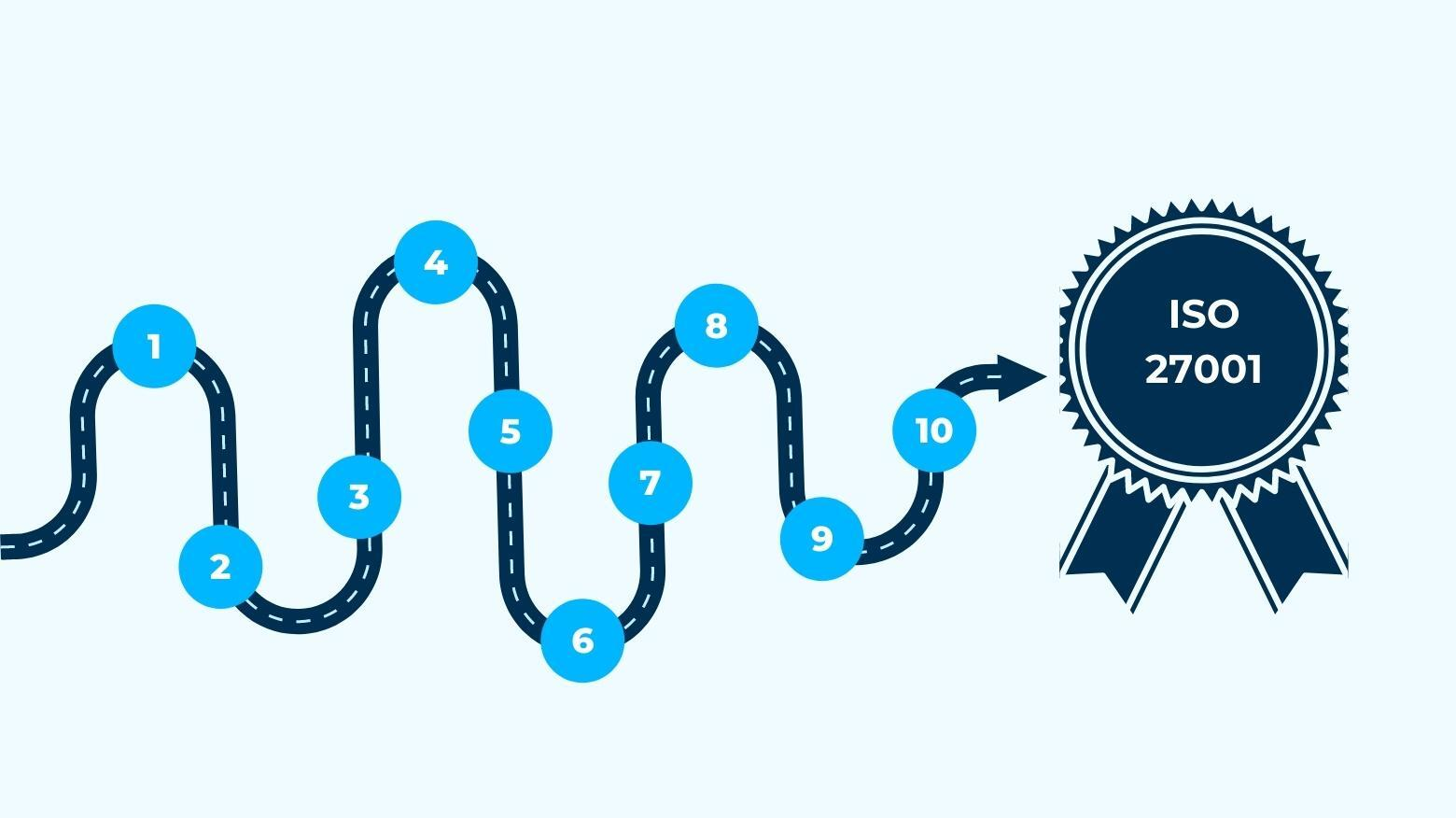
Are you ready for ISO27001 compliance?
Here are a few important steps to get your company up and running and on the road to ISO 27001 certification: 1. Determine when is…
Steps To Implement ISO27001 ISMS
The steps for implementation of ISMS are: Step 1: Form an implementation team – The first step is to select a project manager to oversee…
How an organization achieves ISO 27001 certification?
The length of time it takes for becoming an ISO 27001 certified varies from company to business and is dependent on a variety of variables….
Does ISO 27001 cover Hipaa?
ISO 27001 is a comprehensive and worldwide method to developing and maintaining an Information Security Management System (ISMS), and attaining ISO 27001 registration frequently results…
What is the difference between HIPAA and HITRUST
HIPAA is a law that establishes compliance requirements, and HITRUST is an organisation that assists you in meeting those criteria. The main distinction is that…
What is the difference between ISO 27001 and NIST
The NIST guidelines were created to be flexible and optional. They are reasonably straightforward to adopt in combination with ISO 27001 due to their flexibility,…