- DORA Compliance – A Complete Guide by Valency Networks - 31/01/2025
- Is ICMP Timestamp Request Vulnerability worth considering - 31/12/2024
- Understanding Threat Intelligence in ISO 27001-2022 - 21/11/2024
Title: Cyber Attacks Explained: Network Sniffing
Scope of article
Since we started this series of articles on various cyber attacks, so far we have learnt about denial of service attack and packet spoofing. This month we are going to focus on a wider hacking approach called as network sniffing, which is used very commonly by the prying hackers. We will discuss few tools which are typically used as sniffers, and also discuss in terms of how to protect the IT infrastructure from such attacks.
What is network sniffing?
Sniffing involves inspecting, capturing, decoding and interpreting the information inside a network packet that flows on a TCPIP network. The sole purpose behind this is to steal information, which is very usually in the form of user id, passwords, network details, credit card numbers etc. Sniffing is generally referred to as a “passive” type of attack, wherein the attacker can be silent or invisible on the network. Thus the sniffer is completely non-intrusive which makes it difficult to detect and hence it is a dangerous type of attack. As we already learnt in previous months, the TCPIP packet contains vital information required for two network interfaces to communicate with each other. It contains fields such as source and destination IP addresses, ports, sequence numbers and the protocol type etc. Each of these fields is crucial for various network layers to function, and especially for Layer 7 application that makes use of the received data. By its nature, TCPIP protocol is only meant for assuring that a packet is constructed, mounted on an Ethernet packet frame, and reliably delivered from sender to the receiver across the networks, however it does not contain inherent mechanisms by default, to ensure the data security. Thus it becomes the responsibility of upper network layers to see that the information contained within the packet is not tampered.
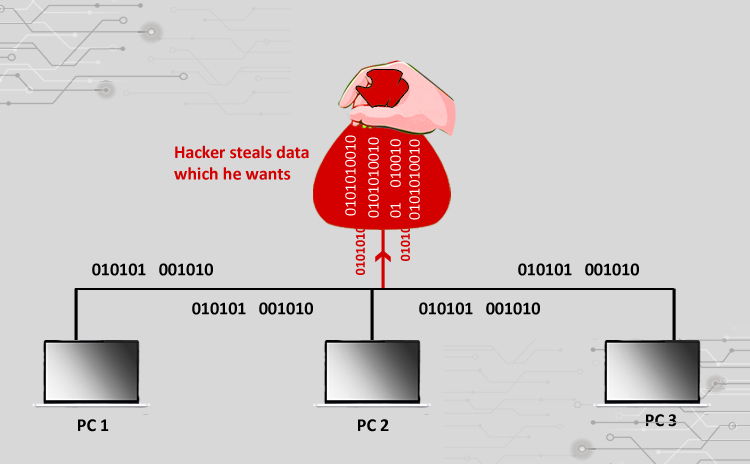
To understand why the hackers sniff, we need to know what they are interested in knowing from the network. Please refer to Fig 1 which shows various information pieces that a hacker can steal or know about, by successfully sniffing a network. The sniffing process is chosen by hackers either to get the data information directly, or to map the network technical details in order to create a further attack. Hackers are always in favor of sniffing because it can be done for longer time duration without getting caught.
How do they “sniff”?
Network sniffing uses sniffer software, either an open source version or a commercial one. While there are multiple ways to sniff a network, broadly there are three ways to do it as shown in Fig 2. It is important to remember that the sniffing process can range from Layer 1 through Layer 7. Talking about physical connectivity, a person who is an employee of a firm, is already hooked up to the internal LAN and can run tools to capture network traffic. Using spoofing techniques, a hacker sitting outside the target network, can intercept packets at firewall level and steal the information. In a latest form of packet sniffing, wide usage of wireless network has made it easy to sit near the network and penetrate it to get information. Regardless of where the hacker is located on the network being sniffed, they use packet capturing or packet sniffer software. Modern packet sniffers which are supposed to be used for troubleshooting network problems, can be used for hacking purpose too, which is another reason why sniffing is so popular among hackers community. Please refer to Fig 3 which depicts the ethical and unethical side of sniffer software. Going into the technical details of how sniffing is done, we need to remember that packet capturing software always runs in promiscuous mode whereby it is capable of intercepting and storing all the packets flowing on a network. This also means that, even though the packet is not meant for the network interface on which the sniffer is running, it is captured, stored and analyzed. Sniffer software contains its own network driver and buffer memory in order to capture a large chunk of packets. Modern sniffers are capable of analyzing the captured packets and convert into a sensible statistical information. Now let’s discuss few ways of sniffing a network to understand how hackers get what they want.
LAN Sniff
A sniffer deployed in an internal LAN can scan entire IP range promiscuously. This helps in providing further details such as live hosts, open ports, server inventory etc. Once a list of open ports is gathered, a port specific vulnerability attack is planted.
Protocol Sniff
This method involves sniffing data related to the network protocols being used. First a list of protocols is created based on the captured data. This is further segregated to create special sniffers for each attack. For example, in a network sniff capture if the ICMP protocol is not seen, it is assumed to be blocked. However if UDP packets are seen, a separate UDP sniffer is started to capture and decipher Telnet, PPP, DNS and other related application details.
ARP Sniff
In this popular method the hacker captures lot of data with an idea to create a map of IP addresses and the associated MAC addresses. Such a map is further used to create ARP poisoning attack, packet spoofing attacks or to dig into router based vulnerabilities.
TCP Session Stealing
This method is a very basic form of sniffing, in which a network interface in promiscuous mode captures traffic between a source and a destination IP address. Details such as port numbers, service types, TCP sequence numbers and the data itself are the pieces which are of interest to hackers. Upon capturing enough packets, advanced hackers can create fabricated TCP sessions to fool the source and destination, and be a man in the middle to take over TCP session.
Application level sniffing
Usually from the data packets sniffed and captured, few intricate application details are found out for information stealing or to create further attacks. As an example, the capture file can be parsed to perform OS fingerprinting, SQL query analysis, application specific TCP port data information etc. In another approach, creating a mere list of applications running on a server is good enough to plant an application specific attack on it.
Web Password sniffing
As the name suggests, HTTP sessions are stolen and parsed for userid and password stealing. While the Secure Socket Layers (SSL) are incorporated for securing on the wire HTTP sessions, there are numerous internal websites which still use standard less secure encryption. It is easy to capture Base64 or Base128 packets, and run a deciphering agent against it to crack the password. In modern sniffers, SSL session can also be captured and parsed for information though this method is not very easy.
Detecting Sniffers
As mentioned earlier, since the sniffers work silently and run in the background, it is very difficult to detect those on a network. There are however few tricks which can provide a clue to a possible sniffer presence. There are two ways to detect sniffer, one being host based and the other is network based. In host based detection, we can use small utilities to detect if the network is running in a promiscuous mode on each host in a network. Since the basic requirement for a sniffer to work is to put the network interface in “read all” mode, disabling it can very effectively help shutting down stray sniffers. In case of network based detection, anti-sniffer software can be run to detect presence of specific signature packets. In another approach, scripts can be run to check each network host for the presence of known sniffers, processes etc. Modern antivirus or antispyware software are capable of detecting sniffing software and disable it.
Protecting from sniffers
While the very first step should be to design a tight perimeter defense system while creating network architecture, there are few methods which could be deployed to make the infrastructure less sniffer-prone. Following tricks help achieve that to a great extent.
Disabling promiscuous mode on the network interfaces results in shutting down most of the sniffer software. This can be done by running an admin script as a daily job on network, or deploying a network policy at the host level to control access to the network card configuration settings.
Using switched networks can reduce the possibility of having a running sniffer on network. Unlike a network hub, in a switched network the packets are delivered to the destination, and are not visible to all the nodes thus reducing the chances of someone sniffing it on the way. Also for the network administrators it becomes easy to detect sniffers by focusing on the switched networks segments, one at a time.
Anti sniffing tools can be used to detect network interface mode as well as various processes and software presence on the servers or network hosts. Modern intrusion detection systems are capable of doing this as their integrated feature.
IPSec encryption can be used for token based packet security in the network infrastructure wherein the data is of confidential nature. IPSec provides data encapsulation and encryption of high standards and is available in modern routers, firewalls and other network components. Almost all operating systems do support IPSec and is widely used in serious IT infrastructure. For session layer protection, SSL and TLS can be used to encrypt traffic.
Protecting FOSS systems
Let us now see a few sniffer products, in order to know what is used in the FOSS world today. Linux systems use tcpdump utility which is an excellent built in sniffer to capture and store TCP packets. As for third party open source tools, wireshark (ethereal) is very famous due to its GUI interface and packet filtering and viewing capabilities. Sniffit, DSniff and Ettercap are similar utilities which are meant for different purposes. DSniff is powerful in terms of capturing SSL traffic.
As for FOSS systems, there is no built-in way to protect themselves from sniffers. The methods described above could pretty much be used for various Linux distros, to make those less-prone. A smart utility available on Linux distros called AntiSniff can be used in a script to detect network interface promiscuous mode.
Summary
Network sniffing involves capturing network packets and parsing those for vital information such as userid, password, TCP sessions etc. Sniffing uses sniffer software tools which are actually meant for network troubleshooting. Since sniffing is a passive type of attack and hence silent in nature, it is difficult to detect it. There are methods to detect and disable network sniffers running on a network and network administrators should incorporate those into their network, in order to protect their IT infrastructure from information loss or theft.
About the author
The author has over 18 years of experience in the field of IT hardware, networking, web technologies and IT security. Prashant is MCSE, MCDBA certified and also F5 load balancer expert. In the IT security world he is an ethical hacker and net-forensic specialist.
Prashant runs his own firm named Valency Networks in India (www.valencynetworks.com) providing consultancy in IT security design, security audit, infrastructure technology and business process management. He can be reached at prashant@valencynetworks.com.
More Relevant Links Below
Web Application Penetration Testing Services
Cloud Application Security Services
Mobile App Penetration Testing Services
REST API Penetration Testing Services
Network Security Auditing Services