- DORA Compliance – A Complete Guide by Valency Networks - 31/01/2025
- Is ICMP Timestamp Request Vulnerability worth considering - 31/12/2024
- Understanding Threat Intelligence in ISO 27001-2022 - 21/11/2024
Title: Cyber Attacks Explained: Man In The Middle
Scope of article
While we are receiving encouraging feedbacks for this series of articles, we thought of bringing yet another attack type for readers. Man in the middle attack is widely used and highly favored by the attackers. Unfortunately many system administrators who should protect their infrastructure from this attack, does not seem to know its severity due to lack of understanding. In this article we bring technical clarity about man in the middle attack and explain ways to protect FOSS infrastructure.
MITM Attack
In one of the previous articles of this series, we learnt about various packet spoofing attacks, and also demonstrated how it can result in to a man in the middle attack. However since this attack is most the favored by hackers, we thought it worth to dedicate an article just for the topic. As the name suggests, man in the middle attack (references henceforth as MITM) is used mainly to steal information and the data valuable to corporate firms. This attack can be made possible by exploiting inherent vulnerabilities of TCPIP protocol at various layers, which makes it dangerous. Technically speaking, it is a derivative of packet sniffing and spoofing techniques and if carried out properly, this attack can be completely transparent to the users, thus making it difficult to detect and stop. MITM attack is sometimes referenced as fire brigade attack, eavesdropping attack, or connection hijacking attack.
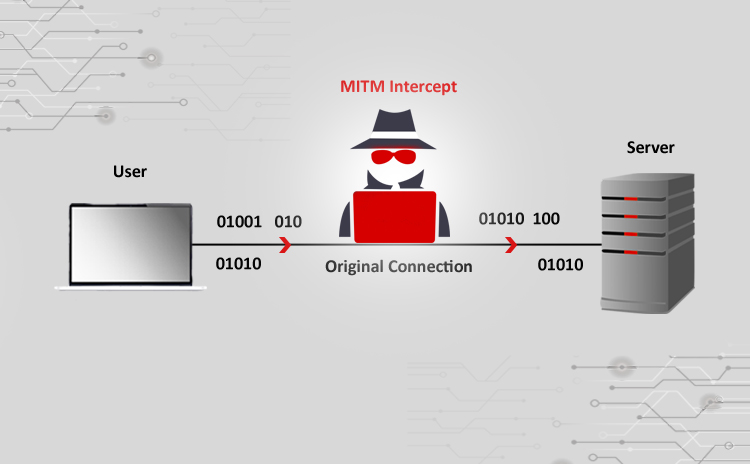
Please refer to Fig 1. At high level, the steps involved main idea behind MITM are, to intercept traffic, break the authentication chain, and impersonate the hacked endpoints seamlessly. The main objective is to steal the session, and thereby the information being transmitted over the wire. As we know, TCPIP works on a three way handshake (SYN, SYN-ACK, ACK). This handshake establishes a connection between two different network interface cards, which then use the packet sequencing and data acknowledgements to send or receive data. The data flows from the physical layer all the way up to the application layer. At layer-2 and layer-3, an Ethernet and IP packet datagram are formed, whereas at the presentation layer the cryptographic SSL session is established assuming that the application is planning to use it. It is important to note here, that each of these layers can potentially participate in the MITM attack.
Fig 2 shows a table which maps the OSI layers to various possible MITM attacks. In order for hacker to steal the session, he needs to use a packet sniffer first. After gathering the packets, he needs to make a choice in terms of which layer to attack in order to gain control, e.g. ARP protocol, or IP or SSL etc. Once the choice is made, hacker then uses advanced tools to inject packets to steal the session and does it so seamlessly that it is transparent to the victims whose session is being hijacked. Although MITM uses IP spoofing at its base, it goes a mile beyond that in order to gain control, by choosing sessions from one or more layers to be hijacked. As an example, the attacker can use ARP spoofing and also cryptographic session stealing to achieve complete control over say an e-commerce transaction. Also as compared to just spoofing the packets, MITM attack modified the intercepted data and re-transmits it over the wire, only this time it makes the victim believe that the packet is legitimate and is coming from a source, which in fact is just another victim.
As for the impact of MITM attack, since it can happen at various layers, the severity of attack can be very high. As an example, an internal employee can use MITM to download HR database being viewed by a fellow HR employee, by stealing the session of the TCP port being used by SQL server and the HR desktop application. In another example, credit card number could be stolen by hijacking a browser session connected to a shopping cart web application. Advanced hackers can steal sessions established at the lower OSI such as Layer-3, to dump all the packets flowing and gain a deep dive insight into applications running on that particular computer, and the usage pattern and other personal details of the person using it. It is also possible to record an entire authentication session, and decipher the userid and password information from it, which can be used by hacker to impersonate the victim and create damage to a greater extent. We again wish to emphasize here, that MITM is a transparent attack and hence should be taken very seriously. The good news is that there are few ways to stop or at least mitigate the impact of this attack which we will soon learn. Now let’s take a look at various MITM attacks which take place at various networking layers.
ARP Poisoning – ARP does the MAC address to IP address translation. In a normal and healthy situation, when a TCPIP protocol stack running on the source computer wants to send a packet to a destination IP address, it first looks into its local cache for a mapping of the IP with a MAC address. If the entry can’t be found, it starts an ARP broadcast asking for a MAC address, for the given IP address. The machine who owns that IP address responds back to the ARP query with its own MAC address. The source then uses it to create the Ethernet frame and starts transmission to that IP. At the same time, the source machine marks the IP to MAC entry in its local cache, so that it could be used to speed up the communication for future requests to the same IP, by avoiding the broadcasts. ARP is a stateless protocol and also the cache does not have its own security mechanism, which results into a serious vulnerability. The underlying mechanism of MITM being packet spoofing and forging, the attacker sends spoofed ARP packets on the local area network, to associate attackers own machine’s MAC address with the IP address of another host which is the target. This forged packet can be as simple as an ICMP packet typically used to Ping a host. The traffic originating for the destination, now in fact reaches attackers machine due to the binding between IP and MAC addresses. Attacker can use the same method to fool another machine, and be able to view communication between both the infected targets, thus making it a local area network specific man in the middle attack. Once the control is achieved, the hacker simply collects the packet from sender, and forwards it to the receiver while recording the packet stream in between. Since there is no data being lost in this whole process, both the victims has no clue about this, thus helping hacker to hide and yet steal the data. ARP poisoning is widely used in internal attacks whereby a smart hacker or evil guy working on the same local area network can steal sessions which results into a data theft.
ICMP MITM – In this method, attacker first pings the whole subnet to find out hosts that are down. It maintains a list of such IP addresses and then waits for those hosts to be accessed or pinged by others. When another machine does so, attacker responds to it by a successful ping response, which prompts other machines to believe that the host is up, and they start communicating with it for the data transfer. At this point attacker responds to TCP handshakes too, and starts collecting the data. Though this is not completely MITM attack, it does play an important role in data theft. To elaborate better, consider if this would happen with an SQL server or a web server, which would result in loosing userid and passwords, thus breaching the corporate security.
DNS MITM – This method is rather rarely used, however it can create a serious security breach. An attacker first sniffs the traffic on a network specifically for DNS queries being made on port 53. The information gathered is analyzed to identify all the DNS servers available on the network. The real attack starts here, by using ARP spoofing to fool the querying machine to send DNS requests to attacker’s computer, rather than the real DNS server. It is a less known fact, that every DNS query contains a unique identification number as a step towards being able to map it to the response received. In order to establish MITM, a query response packet needs to be created that includes this number, but with a bogus query answer. DNS MITM in real life is a tough thing to execute and also time consuming; however it does leave a great deal of insecurity in the network. Please refer to Fig 3 which explains this attack in bit more details. What damage could be achieved at this point is up to hacker’s imagination. As an example, the hacker can divert all DNS queries asking for IP of a web server, to his own IP addresses, thus creating phishing website and steal information. If this attack is planted externally, the damage can actually be beyond imagination. In another form of DNS MITM attack, the attackers puts DNS server under stress by sending a large number of queries, and in the meanwhile intercept its traffic to respond to the DNS queries by bogus responses.
DHCP MITM – Similar to the DNS attack, in this method the DHCP server queries and responses are intercepted. This helps attacker gain complete picture of the network, such as hostnames, MAC addresses, IP addresses and the DNS servers etc. This information is further used to plant advanced attacks to steal the information. Also similar to the DNS attack, an attacker can plant a denial of service attack on a real DHCP server to keep it busy, and in the meanwhile spoof and respond to the DHCP host queries by itself. As we can see, DHCP MITM just acts as a catalyst in the data stealing process, however the impact can further be made severe either by expiring the IP lease on all hosts, thus causing a DHCP broadcast storm on the network, or by assigning same IP to all hosts to cause similar effects. In both of these methods, the network can practically be rendered non-functioning.
So far we talked about the attacks that take place in the crucial areas of TCPIP protocol. Now let us talk about the MITM attacks that can happen from the application usage perspective.
Cookie hijacking – As we know, a cookie is a small piece of text that resides on the user’s machine and stores information related to the website that created it. This is usually done to enhance user experience by remembering his online membership details or profile settings etc. Since this cookie is stored by a browser, it can be accessed by the browser as well as applications. By writing certain cookie stealing scripts or programs, part of whole of the cookie content can be captured, interpreted and presented to the web server, in order to impersonate the user, who now becomes a victim in this scenario. There are three ways to capture the cookie details, either directly accessing it on the computer, or by hijacking the browser session, or by sniffing the web requests and responses transmitted over the wire. Some websites store login session and authentication information in the cookie, which if hijacked can help attacker login to the server without being challenged for userid and password authentication. The problem created by this situation can be as simple as someone’s email account being hijacked, or as severe as someone’s online profile being impersonated, thus resulting into possible monetary loss.
Man in the browser – This is an internet browser attack wherein, a Trojan virus or a malicious script runs in the entity of a browser instance to gain control of the web session. This can be achieved either by exploiting inherent and un-fixed vulnerabilities of an unpatched desktop browser, or by exploiting vulnerabilities which are introduced due to a mis-configuration or non-hardening of the operating system on which the browser is running. Since the attack takes place in the same security context as the user who is using the browser, having security mechanisms such SSL and multi-factor authentication proves to be useless. Multiple operating systems running a variety of browsers exhibit different vulnerabilities, which could be easily exploited by a program written in JavaScript or similar scripting language. To explain the real danger caused by this attack, let’s consider a user who is trying to purchase goods on an internet shopping cart using a browser which is already compromised. User sees what is on the screen and submits the request, however what web server sees is what is actually submitted to it, which can be quite different than what was there on the screen. So if a user is submitting the address where the goods are supposed to be shipped to, the address being submitted can be a fictitious one setup by the attacker to collect the goods, while the user who paid for it will not have a clue about it.
SSL MITM – As we know, the SSL protocol works on the public key cryptography concepts, whereby a server is hosted with a digital certificate for online data encryption, wherein the certificate is provided by some trusted authority such as VeriSign to endorse the identity of the website url. In a healthy situation, when a client such as a browser tries to connect to the secure server, the server provides its certificate to the browser. The browser then checks it against its own list of valid and trusted certificates and verifies the information contained in it. Once the certificate is accepted, the server and browser both negotiate on a common level of encryption to be used, create a key and transfer data in the agreed encryption form. If the certificate is expired or non-trusted, the browser flashes a warning to alert the user who is using it. In order to compromise this situation attacker sniffs the traffic between browser and web server, and inserts his computer in the network by using standard spoofing techniques. From this point onwards, attacker’s computer runs a proxy tool for the SSL communication in such a way that, the web server negotiates SSL key with attacker’s machine, while the communication with browser is pure text. This results in exposing all the sensitive information to attacker’s computer, which is duly sniffed, recorded and stored for malicious usage. In another case, if the attacker gains physical access to the victim computer temporarily, he installs a bogus certificate on it and then uses IP spoofing to divert the traffic. At this point, attacker uses standard spoofing techniques to be part of the game and establishes SSL connection with web server using the trusted certificate and also with the browser using this bogus certificate. This is done to ensure that web address url is seen as HTTPS, and the actual communication is indeed SSL helping hacker to hide, but the data is being stolen in the process.
Wireless MITM – Similar to the wired attacks, in case of wireless networks the data stealing can actually be bit easier. It exploits the design vulnerabilities in the Wi-Fi networks whereby a dummy access point is setup in the network carrying same SSID signature and a stronger signal. The next step is to disrupt client traffic to the real legitimate wireless router, either by spoofing or by subjecting router to the denial of service attack using a packet storm. Once the router gives up, a wi-fi connection is established by the dummy router which starts the packet sniffing and data theft. There are few other ideas such as logging into the real router by using a brute force method and create a wireless bridging with the dummy router, or to fake the MAC address of real router to fool and lure the Wi-Fi clients to dummy router etc. Due to the usage of wireless signals, it is unfortunately possible for hacker to steal data and at the same time be undetected almost forever. Due to lack of knowledge, it is very common to have wireless routers at home or in the network which are not configured correctly or not secured using appropriate keys or passwords.
Other MITM Attacks – It is important to note that MITM attacks are possible in the critical networking components as well as new technologies. Routers and managed switches can be spoofed to create a higher security impact, and also the firewalls can be fooled to deliver legitimate traffic to a rough machine. Technologies such as mobile computing and Bluetooth are vulnerable to MITM attacks however those are out of scope for this article.
Protecting FOSS systems
While the MITM attack is a difficult one to tackle, there are few preventive mechanisms that every network administrator should adopt in their infrastructure. Since the heart of MITM attack is packet sniffing and spoofing, utmost care needs to be taken while designing the network to introduce network monitoring points. Using intrusion prevention systems proves to be a very good choice for large corporate where the network is complex and hence more susceptible to MITM. Since this attack exploits the inherent vulnerabilities of unprotected TCPIP protocol, techniques such as IPSec security can be used to ensure traffic authentication at a lower OSI layers.
For a datacenter hosting FOSS systems, the very first thing to implement is MAC address security. This can be achieved by choosing host based model, or configuring the managed switches and DHCP systems appropriately. To protect DNS systems, one can use DNSSEC which digitally signs each DNS query request and its response, thus endorsing its legitimacy. In case of very critical IT infrastructures, using manual hosts’ entries instead of DNS servers can actually help fix DNS hijacking problems. For FOSS based web infrastructures, using stronger ciphers implemented around TLS technology instead of SSL are suggested. Also a properly authenticated session management and client side authentications such as client certificates should be used. Another idea is to use multi-factor authentication implemented on secure protocols. As we learnt earlier, MITM attack planted on a browser can bypass all these securities, hence it is important to implement best secure coding practices to deal with situations in the web applications.
Linux FOSS systems come with a built in, but usually less known feature called as the source address verification. It is a kernel feature which when turned on, starts dropping packets which appear to be arriving from the internal network, but in reality are not. Most of the latest kernels such as Ubuntu and CentOS etc, do support it, but if your Linux distro does not support, it is the time to upgrade it. Modifying hosts.conf file to add “nospoof on” is another level of defense to try. In terms of detection, for smaller Linux networks a nice utility called arpwatch is very useful. Arpwatch keeps track of MAC and IP addresses and it records all changes and can be scripted to alert administrators upon a possible attack. Scripting can also be done to go through network interface logs and look for anomalies in terms of source address forging.
Summary
MITM is really a difficult type to tackle and hence should be taken seriously by IT management. It can result in data theft causing severe reputational and monetary losses to the corporate firms. As a bottom-line, having a correctly defined security perimeter defense design, server and network component’s hardening, implementing robust patch management system and following best security practices can help fix MITM attacks. Since this attack may not be visible, being vigilant in terms of network problems and performance always helps detect it, before a data theft can occur.
About the author
The author has over 18 years of experience in the field of IT hardware, networking, web technologies and IT security. Prashant is MCSE, MCDBA certified and also F5 load balancer expert. In the IT security world he is an ethical hacker and net-forensic specialist.
Prashant runs his own firm named Valency Networks in India (www.valencynetworks.com) providing consultancy in IT security design, security audit, infrastructure technology and business process management. He can be reached at prashant@valencynetworks.com.
More Relevant Links Below
Web Application Penetration Testing Services
Cloud Application Security Services
Mobile App Penetration Testing Services
REST API Penetration Testing Services
Network Security Auditing Services