A Comprehensive Comparison of OWASP ZAP and Burp Suite Vulnerability Assessment Tools (Part 1) Introduction OWASP ZAP (Zed Attack Proxy) and Burp Suite are two…
Importance Of Cyber Security Threat Detection
In today’s digital age, the threat landscape is constantly evolving, making it crucial for individuals and organizations to prioritize threat detection. By staying one step…
Difference between PII and PHI and ePHI
PII, PHI, and ePHI are all related to data privacy and security, particularly in the context of sensitive information in various industries like healthcare and…
SCADA Security Hacking Story: New York Dam
In 2013, an incident occurred in New York involving the intrusion of Iranian hackers into a small dam known as Bowman Dam. While the nature…
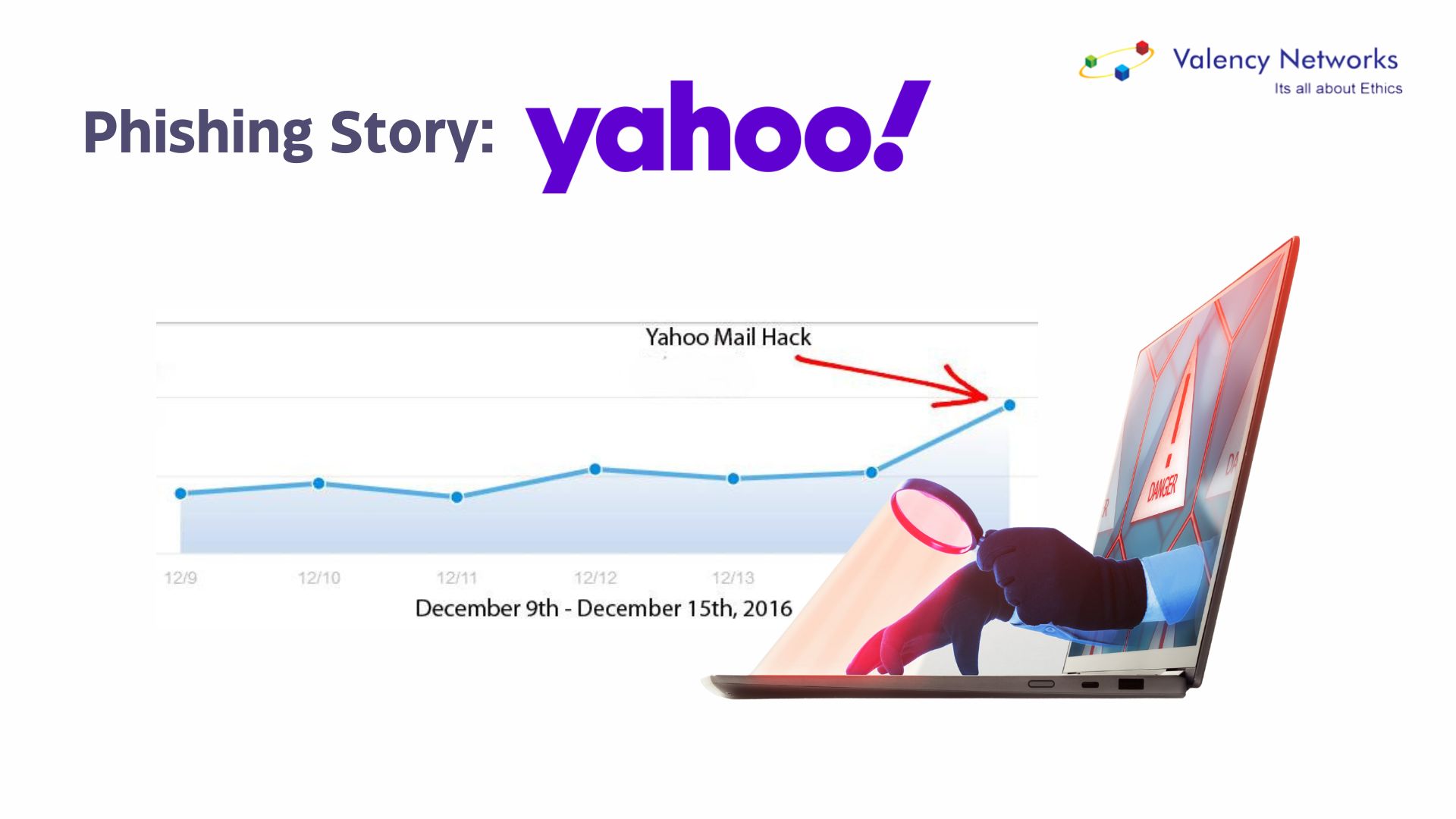
Phishing Story: Yahoo
In 2016, a primary email service provider, Yahoo, experienced one of the most significant data breaches in history. The breach, which occurred in 2014 but…
SCADA Security Hacking Story: Target Stores
SCADA system attacks typically occur through an organization’s business network, impacting the remote control systems. However, in 2013, hackers took a different approach by targeting…
SCADA Security Hacking Story: Stuxnet
In 2010, Stuxnet emerged as one of the most intricate malware ever discovered. It infiltrated control system networks, leading to speculations that it severely impacted…
Phishing Story: Twitter
In 2017, a central social media platform, Twitter, fell victim to a large-scale phishing attack that compromised the accounts of several high-profile individuals and organisations….
Phishing Story: Target
In 2014, a major U.S. retailer, Target Corporation, experienced a massive data breach that affected millions of its customers. The breach was initiated through a…
Phishing Story: SBI
In 2018, one of India’s largest banks, the State Bank of India (SBI), faced a significant phishing attack targeting its customers nationwide. The attack aimed…