- DORA Compliance – A Complete Guide by Valency Networks - 31/01/2025
- Is ICMP Timestamp Request Vulnerability worth considering - 31/12/2024
- Understanding Threat Intelligence in ISO 27001-2022 - 21/11/2024
Title: Cyber Attacks Explained: Packet Spoofing
Scope of article
Last month we started this series of articles to cover important cyber attacks which impact critical IT infrastructure in organizations. The first one in the series was the denial of service attack which we discussed in details. This month we are going to learn about the packet spoofing attack which is found to be a favorite of the hackers and widely being used in exploiting network vulnerabilities. We are also going to discuss how this type of attack affects Linux systems and understand how to mitigate the risks.
How packet spoofing works?
Spoofing by definition means to imitate or trick someone. To understand spoofing attack we need to examine the IP packet structure in details. Many cyber attacks stem out of design flaws in the fundamental network designs and the packet spoofing attack is not an exception to that. Please refer to Fig 1. As we know, a basic Ethernet network packet is essentially a data chunk with various pre-defined fields such as source and destination MAC addresses, frame checksum code, preambles etc. In case of TCPIP protocol, the TCP frame encapsulates the IP datagram, and both piggyback on the basic Ethernet packet. TCP part provides the connection oriented sense, while the IP packet contains source and destination addresses and ports. It is the duty of various OSI layers to contribute their bits towards the formation of a complete packet.
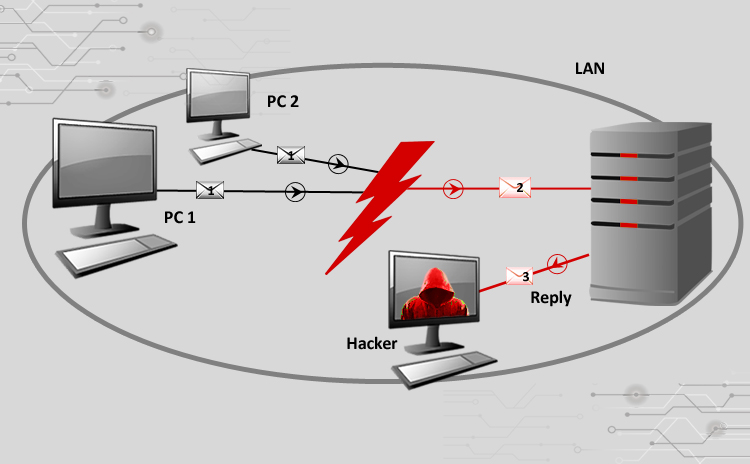
As we learnt last month, TCPIP works on a three way handshake (SYN, SYN-ACK, ACK). This handshake establishes a connection between two different network interface cards, which then use the packet sequencing and data acknowledgements to send or receive data. The conversation is formally concluded by using a FIN/FIN-ACK handshake. The source and IP address field values decide who is talking to whom; while the port fields decide which source application is talking to which destination application. IP address fields in the IP packet are filled up automatically by the upper layers behind the scene, however malicious users or programs can modify these fields and this is exactly where the spoofing comes in to the picture. Please refer to Fig 2. In a very simple type of packet spoofing attack, the hacker creates IP packets targeting a destination; however the source IP field is modified so that it does not reflect IP address of the hackers’ computer, but in fact of some other computer, which can be used as a data collector or a sniffer by the hacker. By its design, the TCPIP stack running on destination computer is supposed to respond back to the source IP of the received packet, and upon doing so; the sniffer computer receives the packet. With that said, if a packet monitoring software is run on the destination computer, it will show that the packets are coming from this sniffer computer, which in reality is not the case. Thus the hacker is successful in hiding himself and at the same time collect packet information from the sniffer computer, because his own real source IP is nowhere revealed in this process.
Now let’s understand why hackers prefer spoofing. While hiding on the network is the very first step, hacker’s intention is always beyond that. By collecting packets on the sniffer computer, hackers can gain a lot of information about the destination target machine. Vital information such as open ports, type of operating system, layer 7 applications, cryptography types used etc can be collected while not revealing the self identity. Just as an example, a hacker can send spoofed packet to find out if the target is running a web server. Once the port information is revealed on the sniffer, another chunk of spoofed packets can be sent to target to establish telnet session and check web server headers which would reveal OS information as well as web server type and the security support information. Please note that the hacker need not always have access to the sniffer machine, in fact using an advanced packet sniffing tool can help attacker use only his own machine, send spoofed packets, collect data on the same machine and still be invisible on the network from attack standpoint.
Advanced hackers can use spoofing to find out state of a firewall too. As we know, the firewall is a state-full packet filtering process which works on a set of configurable rules to decide which packet should be allowed and which should be dropped. When a source machine tries to connect to another machine which is protected behind a firewall, the source machine has to first establish a TCP handshake with the firewall. If the connection is allowed, the firewall itself establishes another connection with the destination machine and the data transfer occurs with the firewall as a catalyst in this whole process. Also when the destination machine tries to send acknowledgement to the source, the firewall is bound to intercept and check whether or not a corresponding request from source is pending. If it is not the case, the packet is dropped. All this is true for modern firewalls which are state-full, but not in case of firewalls which are old or cheap, which tend to allow the ACK packets thus exposing the spoofing possibilities.
There are three reasons worth mentioning here which typically make a network vulnerable to spoofing attacks. The first being, the IP packets can be modified very easily using free utilities available. The second reason is that even today many applications still use source and destination IP address combination as a secure way of authenticating a packet. Just as an example, there are web servers which allow or disallow HTTP requests from a list of configurable IP addresses. Such systems prove to be useless if the packet is spoofed to reflect an IP address which is in the list of allowed IPs. The third reason is, the routers forward traffic based on destination address and by default do not care much about the source address.
Packet Spoofing Types
With this basic knowledge of how spoofing works, let us now dig a bit further into details. At a broad technical level, there are two basic types of spoofing namely blind spoofing and non-blind spoofing. As we discussed earlier that the packet sequence number and acknowledgements help data transfer, sensing those fields is an important requirement of a spoofing based attack. In the blind spoofing type, the attacker sends multiple packets to the target to sample the sequencing numbers. Once the pattern is found out, it becomes easy for attacker to create another set of spoofed packets to collect data being transferred. Whereas, in the non-blind type the attacker must be on the same subnet as the target, to be able to easily see the sequencing numbers and acknowledgments. Once he gets his hands on it, he can break the established connection between target and the other computer to which it is talking to, and re-establish connection by modifying the sequence numbers to that of the attackers own machine. An extended version of this type is man in the middle attack whereby an entire session is stolen to decipher and steal data.
Now let’s take a look at how basic concept of spoofing could be used by hackers to impact various TCP based application services.
IP Port spoofing: In this type, the source port is modified in order to cheat the NAT devices and firewalls, also to hide deep in the network. A firewall which is not very well managed can end up leaving stale rules in action, which can potentially lead certain outgoing ports on certain IP addresses to be open. IP port spoofing attack takes advantage of this situation. This is a serious attack because the hacker can be outside the network and still be able to look at internal traffic.
ARP spoofing: Since it is all about modifying or forging packets, modern attackers don’t restrict themselves to IP fields. In this type which is also known as ARP poisoning, the attacker sends spoofed ARP packets on the local area network, to associate attackers own machine’s MAC address with the IP address of another host which is the target. Due to this, the traffic originating for the destination, now in fact reaches attackers machine due to the binding between IP and MAC addresses. Thus this becomes a local man in the middle attack. The attacker can further hide by forwarding received data to the actual destination, and since there is no data lost in this process, it is almost impossible to find the man stealing the data in the middle.
DNS spoofing: Also known as DNS poisoning attack, this is a serious type wherein the domain name system server is spoofed to alter entries of domain names to reflect attackers IP address. This results in sending web or email traffic to attacker’s machine, when someone tries to access the domain name. This attack is achieved by creating multiple forged packets wherein the IP, port and service type entries are modified to serve the purpose. The repercussions of such an attack are very dangerous, whereby a website can be defaced or email data can be stolen.
Email and Web spoofing: Speaking about layer-7, the same technique of impersonation can be stretched to crafting fake email addresses and web requests and hyperlinks. This is usually done to plant a Trojan or a virus and spread it across. Please remember that spoofing is a basic component in planting a denial of service attack, mainly because the attacker would always want to hide behind the curtains.
Protecting FOSS systems
While the spoofing attack is a difficult one to tackle, there are few preventive mechanisms that every network administrator should adopt in his infrastructure. Since the spoofing starts at layer-2, the real protection has to be implemented in the critical network components such as routers, firewall, switches etc. Deploying a latest state-full firewall and enabling features in it which fight against source packet spoofing can be first level of defense. As a daily chore, network logs from firewalls, routers and switches can be parsed using a script to see if multiple duplicate ACK packets are being generates. Also if an unusual number of SYN packets are being observed which are not being responded back, that could lead as a clue to spoofing. The real spoofing detection is to check a bunch of packets for a given set of source and destination IP addresses and see that there is no other IP address involved in that communication session. This is a difficult task for a script program to achieve and for complex networks, deploying an intrusion detection device usually helps to a great extent. There is a thumb rule while inspecting packets that in a network packet log, if an internal LAN IP address is being shown in the log file capturing data for an external interface, then that is a problem.
Linux FOSS systems come with a built in, but usually less known feature called as the source address verification. It is a kernel feature which when turned on, starts dropping packets which appear to be arriving from the internal network, but in reality are not. Most of the latest kernels such as Ubuntu and CentOS etc, do support it, but if your Linux distro does not support, it is the time to upgrade it. Modifying hosts.conf file to add “nospoof on” is another level of defense to try.
In terms of detection, for smaller Linux networks a nice utility called arpwatch is very useful. Arpwatch keeps track of MAC and IP addresses and it records all changes and can be scripted to alert administrators upon a possible attack. Scripting can also be done to go through network interface logs and look for anomalies in terms of source address forging.
Summary
Packet spoofing is a difficult type of attack to tackle. It can result in serious data loss and there are ways to detect it and stop it. Configuring firewalls, switches and routers is an important step to prevent networks from spoofing and the network administrators should know about it. Finance firms are found to be common victims to this attack and their IT management should take necessary steps to prevent firm’s reputational or monetary loss. Implementing IPS devices certainly helps in getting control over the IT network infrastructure security.
About the author
The author has over 18 years of experience in the field of IT hardware, networking, web technologies and IT security. Prashant is MCSE, MCDBA certified and also F5 load balancer expert. In the IT security world he is an ethical hacker and net-forensic specialist.
Prashant runs his own firm named Valency Networks in India (www.valencynetworks.com) providing consultancy in IT security design, security audit, infrastructure technology and business process management. He can be reached at prashant@valencynetworks.com.
More Relevant Links Below
Web Application Penetration Testing Services
Cloud Application Security Services
Mobile App Penetration Testing Services
REST API Penetration Testing Services
Network Security Auditing Services