- Are you ready for ISO27001 compliance? - 01/04/2023
- Steps To Implement ISO27001 ISMS - 01/04/2023
- How an organization achieves ISO 27001 certification? - 01/04/2023
Soon when the world went in lockdown during pandemic all the business around world made strategies to ensure business continuity and not many but few focused their efforts on security as well.
During pandemic all IT and non-IT industries focused on security in employee connecting to company networks remotely or remote accessing of networks. But critical components missed out were:
- 1. Data at rest and
- 2. Data in transit
All business and companies use various applications and tools either 3rd party or self-developed. Think of an in-house developed project collaboration and project management tool hosted either on a local server or Cloud. In pandemic hackers were luring for data stealing like bees for honey in spring. And while industry was focused on securing VPN and other technical fixations, what was left easy and unprotected for hackers were following attack vectors that lead to web hacks network hacks and cloud exploitation.
- 1. Insecure and vulnerable web application
- 2. Unpatched and un-hardened web server
- 3. Unreliable certificate deployment on web server
- 4. Unauthenticated exposed API’s
- 5. Malicious or not-in-use services running on server on cloud
What this report is all about?
We at Valency Networks caters to a variety of services to our customers, ranging from vulnerability assessment and penetration testing to information security compliance services. With a global base of great customers, we end up finding a great deal of security issues and security postures of their organizations. This report contains a gist of all those findings. We took a great deal of samples from all the testing performed in the year 2020, such as VAPT of Web applications, static security analysis of Android and iOS applications, Exploiting of network infrastructure and ISO27001, HIPAA, GDPR, and SOC2 related vulnerability assessments etc.
We felt like sharing this report for a sole reason to generate awareness. By spending years in cyber security domain, Valency Networks has very well understood that there is not enough awareness and seriousness about this domain in the industry. This is unfortunately true irrespective of countries, cities, industry sectors or the job roles that cater to the domain. By distributing these statistics Valency Networks wants to send a message to all industries, that the cyber security needs to be taken very seriously and apt care is an immediate need.
This report does not contain any ready-made material from internet or any other survey. It is generated by using the factual data gathered by Valency Networks, while catering to its customers. The numbers, graphs and statistics shared in this report are copyright of Valency Networks. As a reader you are encouraged to read, understand and follow this report for your own benefit, and get a consent of Valency Networks if you want to use material and data contained in this report, for your own reporting or any other purpose of presentations.
Narration on “Cyber security learnings this year”
Year 2020 was a strange and yet very educating year for cyber security professionals. Due to COVID19, all industries started being introspective about their own cyber security posture. It was also a sharp learning curve for Valency Networks. A Top 10 cyber-attacks gist as seen by Valency Networks team is mentioned below:
- 1. Web applications saw new types of attacks which are beyond the ones listed on OWASP Top-10
- 2. Web server level attacks increase exponentially, in order to take control of the entire server
- 3. Companies because more serious about ISO27001 and ISO13485 compliances
- 4. Fintech companies saw higher rate of REST API injection type of attacks
- 5. Healthcare companies saw increased rate of Android app based attacks
- 6. Internal patching is still a big problem for vulnerabilities within a LAN
- 7. Corporate networks saw more attacks on the VPNs and firewalls
- 8. Loose firewall policies helped attackers spread ransomeware
- 9. Firewall rule bypassing increased to a large extent
- 10. IoT attacks increased to some extent
Keeping technical observations away, following learnings are also a key to a better cyber security assurance.
- 1. Cyber-attack are not restricted to IT industries but we saw financial services, retail, manufacturing, healthcare, professional services been victims in 2020 and can be targets in 2021 too.
- 2. Cyber-security should to be a CEO, CFO level matter and not just IT or Cloud Ops
- 3. Advanced risk analysis and monitoring methodologies is need for every business
- 4. Email literacy should be uplifted, since with pandemic our lives have gone online more than ever before
- 5. Weak end-point protection can hit big on pockets along with negligence towards Cloud and network can bring-in law-suit or reputational damage.
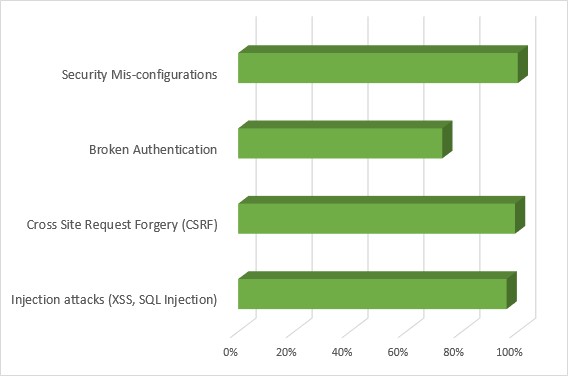
Statistics: Web Attacks
| Sample size | 150 |
| Injection attacks (XSS, SQL Injection) | 96% |
| Cross Site Request Forgery (CSRF) | 99% |
| Broken Authentication | 73% |
| Security Mis-configurations | 100% |
Statistics: Server Attacks
| Sample Size | 100 |
| Missing Patches | 99% |
| Missing End Point Security | 83% |
| Missing Continuous VAPT | 87% |
| Access Control Vulnerabilities | 64% |
| Stray Services | 42% |
| Missing Cyber Monitoring | 94% |
Statistic: Top 5 Vulnerable Ports
| SSH | TCP 22 |
| SSL | TCP 443 |
| FTP | TCP 21 |
| MSSQL | TCP 1433 |
| Site to Site VPN | UDP 500 |
Which industries got attacked the most?
Below is a list of industries whom we catered to for cyber security services. The list is in the descending order, which means that the first industry sector in the list was the most hacked one.
- 1. Manufacturing industries going for IoT implementation
- 2. Healthcare industries creating medical devices and software
- 3. IT Product companies hosting their SaaS applications
- 4. Fintech companies having their mobile applications
- 5. IT Services companies who remote into their customer’s infrastructure
What should organizations do to be cyber resilient?
Do not hide behind tools i.e. IDS, IPS or DLP. Most basic and apt thing to do is communicate with all your employees about cyber-security and being cyber resilient. Every two out of three businesses saw insider attack and threats in year 2020. Being communicative on cyber incidents and providing pointer on how to protect or prevent against cyber-incidents makes employee more on-guard and watchful!
Your list of actionable To-Do for being cyber-secure resilient:
- 1. Be Communicative about latest cyber-fraud & share protection against them
- 2. Enable 2 Factor authentications more
- 3. Secure your WiFi, VPN, LAN/WAN networks for data in transit
Additional Observations
- Phishing attacks are increasing drastically. Valency Networks gets many requests of cyber forensic cases to handle wherein the root reason is phishing. A great deal of phishing awareness is required.
- Ransomeware attacks are increasing too. Most of those are stemming out of incorrect firewall configuration, and inadequate patching. A good discipline via ISO 27001 compliance is required to be implemented.
- Cloud server attacks were found to be at its maximum in 2020, as analyzed by Valency Networks team. Most of the attacks were due to incorrect or missing cloud infrastructure configuration that resulted into stealing of data by attackers
.
What this year taught us?
Year 2020 was a roller-coaster ride for sure. It certainly taught us many thing in our professional and personal life, such as below.
• When we are working from home, its important to remember that hackers are also working from home, and with the same enthusiasm.
• Cyber security starts at management level in any organization. A correct strategy and adequate funding is important to ensure that the business runs without any glitches.
• Healthcare sector and IoT have a lot to do besides just the vulnerability assessment and penetration testing or implementation of HIPAA or GDPR.
• A pandemic such as COVID19 is certainly a problem to the humanity but it is also an opportunity to look at our own cyber security at a personal level, and also that of our family. This boils down to whether we are using safe web applications or mobile applications, is our personal data safe, are we enough aware about phishing and whaling attacks etc.
References
-
1. Why Manufacturing Industry is Prone to Ransomware Attacks (https://www.valencynetworks.com/blogs/why-manufacturing-industry-is-prone-to-ransomware-attacks/)
-
2. Why Hackers Like The Healthcare Industries (https://www.valencynetworks.com/blogs/why-hackers-like-the-healthcare-industries/)
-
3. Vulnerability Assessment – Automated v/s Manual Testing (https://www.valencynetworks.com/blogs/vulnerability-assessment-automated-v-s-manual-testing/)
-
4. Top 5 Reasons To Perform VAPT Of Your Web Application (https://www.valencynetworks.com/blogs/top-5-reasons-to-perform-vapt-of-your-web-application/)
-
5. GDPR Compliance for Mobile Apps (https://www.valencynetworks.com/blogs/gdpr-compliance-for-mobile-apps/)
-
6. Why HIPAA and GDPR cannot replace each other (https://www.valencynetworks.com/blogs/why-hipaa-and-gdpr-cannot-replace-each-other/)
This report can be downloaded at https://www.valencynetworks.com/pdf/Cyber-Security-Year-2020-Statistics-Report-Valency-Networks.pdf
