- SCADA Security Hacking Story: New York Dam - 24/07/2023
- Phishing Story: Yahoo - 17/07/2023
- SCADA Security Hacking Story: Target Stores - 13/07/2023
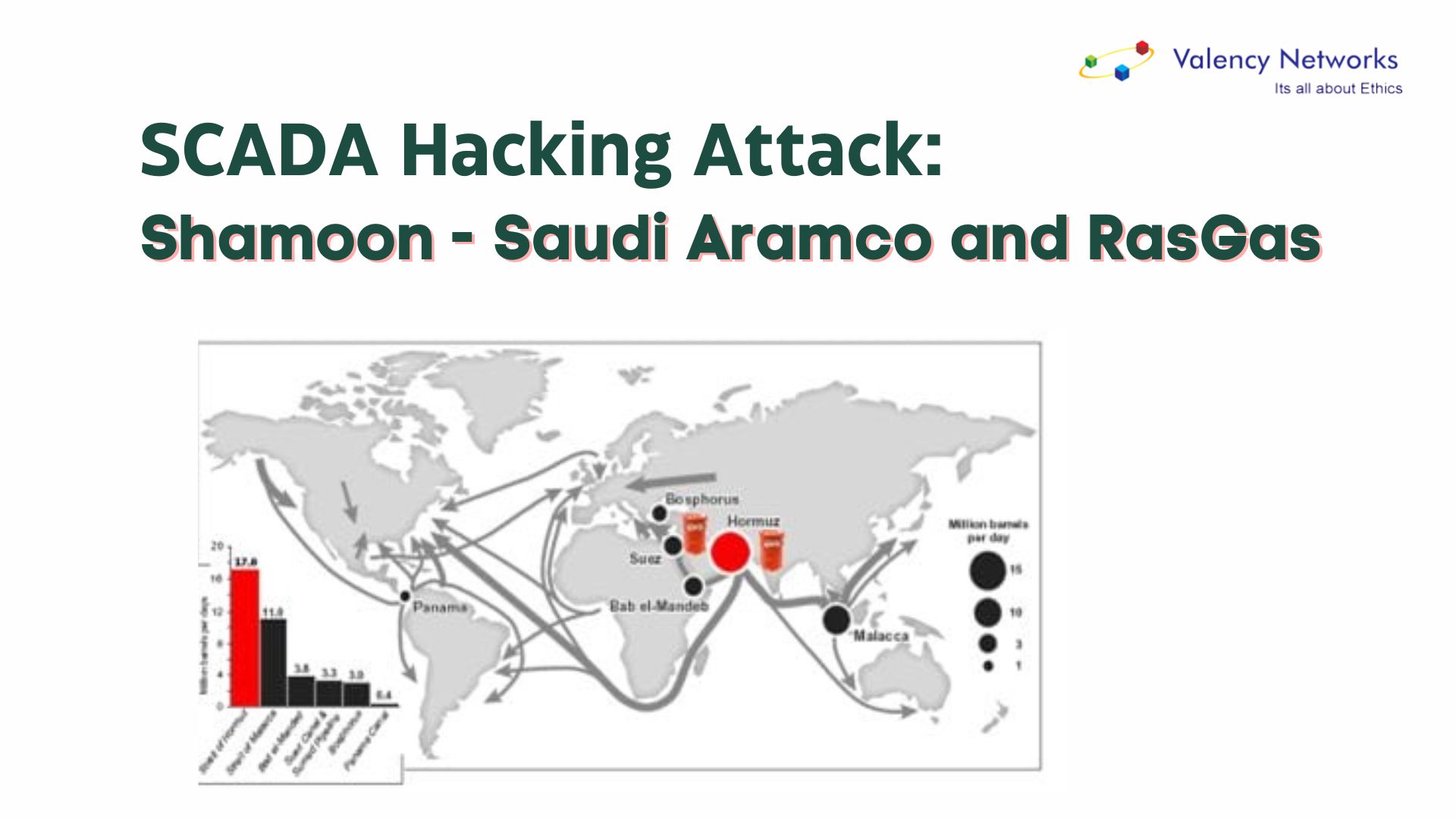
In 2012, Saudi Aramco, the prominent global energy company, encountered a severe and unprecedented cyber incident that sent shockwaves through the industry. The company fell victim to a malicious software attack known as Shamoon, which was a devastating assault on its computer systems. This nefarious malware, infamous for its dual functionality of information theft and destruction, wreaked havoc by overwriting critical data on over 30,000 computers with a haunting image of a burning American flag.
Not only did Saudi Aramco suffer the consequences of this cyber onslaught, but another significant target also felt its impact. RasGas, a leading Qatari natural gas company and an essential player in the liquefied natural gas (LNG) sector, found itself at the mercy of the Shamoon malware’s destructive tendencies. The attack on RasGas sent shockwaves through the industry, underscoring the vulnerability of even the most prominent energy corporations.
Fortunately, amidst the chaos caused by Shamoon, Saudi Aramco and RasGas were spared the complete devastation of their SCADA (Supervisory Control and Data Acquisition) systems. SCADA systems are critical for managing and controlling industrial processes, including energy production and distribution. Although the malware attempted to propagate through local networks, it failed to infiltrate and directly impact these vital control systems.
The ability of Saudi Aramco and RasGas to recover from such a destructive cyber-attack stands as a crucial lesson to the broader energy sector and organisations worldwide. This incident highlights the necessity of implementing robust cybersecurity measures and preparedness strategies to defend against increasingly sophisticated threats. The aftermath of the Shamoon attack prompted a reevaluation of security protocols and emphasised the importance of proactive defences and effective incident response plans.
The impact of this malware attack went beyond the immediate financial losses and operational disruptions suffered by the targeted companies. It sent ripples across the energy industry, raising awareness about the escalating cyber risks critical infrastructure sectors face. The incident served as a wake-up call, urging governments, businesses, and organisations to enhance their cybersecurity capabilities to safeguard against similar threats.
Since the Shamoon attack, the global cybersecurity landscape has rapidly evolved. Companies across various sectors have recognised the need to fortify their digital defences, investing heavily in advanced technologies and threat intelligence. Collaborative efforts between industry stakeholders, government agencies, and cybersecurity experts have led to improved information sharing, incident response coordination, and the development of innovative defensive strategies.
The lessons learned from the Shamoon attack remain pertinent as the energy industry continues to embrace digital transformation and rely on interconnected systems. It underscores the importance of maintaining resilient infrastructure, staying vigilant against emerging threats, and fostering a cybersecurity culture prioritising prevention, detection, and mitigation.
In an ever-evolving digital world, the resilience and adaptability demonstrated by Saudi Aramco and RasGas in the face of the Shamoon malware attack serve as a reminder that organisations must remain proactive, prepared, and resilient to navigate the treacherous cyber landscape. The story of Shamoon serves as a powerful cautionary tale, compelling businesses worldwide to bolster their cybersecurity measures and fortify their defences against the relentless onslaught of cyber threats.
Why choose Valency Networks for Cyber Security?
We claim to be the ultimate defender in the realm of cyber security. Allow us to give a brief overview to support our claim:
- Expertise: Valency Network has worked with the world’s top IT service and product companies to implement various cyber security services. We have customers worldwide, and they rate us as the leading Cyber Security Company for our dedication and subject matter expertise.
- Comprehensive Solutions: Valency Networks offers a complete suite of cybersecurity services comprising Risk Assessment, Compliance, Risk Management and Risk Solutions. We deliver cutting-edge solutions in Vulnerability Assessment and Penetration Testing services for IT Networks, Web apps, cloud apps, mobile apps and IoT/OT networks. We also provide Cyber Security Consultancy Services, Compliance Implementations and Cyber Security Auditing Services for ISO27001, FISMA, HIPAA, GDPR, SOC2, PCI-DSS, Cyber Essentials, PIPEDA, TISAX, etc.
- Innovation: Valency Networks uses the latest technology and innovative approaches to address emerging challenges in the ever-evolving cyber landscape.
- Reputation: Recognised as one of India’s top cyber security companies, we have been accoladed as “The Top Cyber Security Company of India” for our excellence in delivering effective and reliable security solutions.
- Client-Focused Approach: We take our customer data security very seriously, which has helped us establish ourselves as a country’s top cyber security expert by gaining our customer’s trust and loyalty. We work closely with clients, catering to their needs and ensuring maximum protection and assurance.
Hence, regarding cyber security, Valency Networks is the trusted armour that safeguards your business, allowing you to navigate the digital world confidently.
How can Valency Network help you prevent SCADA Security hacking attacks?
Valency Network offers various services and solutions to help organisations prevent SCADA security hacking attacks. Here are some ways in which we can assist:
- Vulnerability Assessments and Penetration Testing: Valency Network can comprehensively assess your SCADA systems, identifying vulnerabilities and weaknesses that hackers could exploit. Through penetration testing, we simulate real-world attack scenarios to evaluate the effectiveness of your security controls.
- Risk Assessment and Mitigation: Valency Network can perform risk assessments tailored to your SCADA environment, identifying potential threats and their impact on critical infrastructure. Based on the findings, we can develop and implement strategies to mitigate risks and enhance the security posture of your SCADA systems.
- Security Architecture and Design: Valency Network can help design secure SCADA architectures, taking into account best practices and industry standards. We can assist in developing fast network segmentation, access controls, and encryption mechanisms to protect critical assets.
- Security Monitoring and Incident Response: Valency Network can deploy advanced monitoring solutions to detect and respond to real-time security incidents. We can set up Security Information and Event Management (SIEM) systems, Intrusion Detection Systems (IDS), and Security Operations Centers (SOC) to continuously monitor SCADA systems and respond swiftly to potential threats.
- Employee Training and Awareness: Valency Network recognises the importance of human factors in cybersecurity. We can provide customised training programs and awareness campaigns to educate employees about SCADA security best practices and social engineering risks and recognise and report potential security incidents.
- Compliance and Regulatory Assistance: Valency Network can help your organisation navigate SCADA security compliance requirements and regulatory frameworks. We can assist in aligning your systems with industry standards such as NIST, IEC 62443, and ISA/IEC 62443, ensuring adherence to relevant regulations and guidelines.
- Incident Response Planning and Exercises: Valency Network can collaborate with your organisation to develop robust response plans tailored to SCADA security incidents. We can conduct tabletop exercises and simulations to test the effectiveness of your response strategies and refine them as necessary.
Thus, our expertise and services encompass vulnerability assessments, risk mitigation, security architecture design, monitoring, incident response, employee training, compliance assistance, and incident response planning. By leveraging these services, you can enhance your SCADA security defences and proactively prevent SCADA security hacking attacks. So please sit back and relax, knowing we have your back as a trusted cyber security ninja to guide you in this ever-changing digital world.